stuxnet
Stuxnet is a malicious computer worm believed to be a jointly built American-Israeli cyber weapon.[1] Although neither state has confirmed this openly,[2] anonymous US officials speaking to the Washington Post claimed the worm was developed during the administration of Barack Obama to sabotage Iran’s nuclear program with what would seem like a long series of unfortunate accidents.[3]
Stuxnet specifically targets PLCs, which allow the automation of electromechanical processes such as those used to control machinery on factory assembly lines, amusement rides, or centrifuges for separating nuclear material. Exploiting four zero-day flaws,[4] Stuxnet functions by targeting machines using the Microsoft Windows operating system and networks, then seeking out Siemens Step7 software. Stuxnet reportedly compromised Iranian PLCs, collecting information on industrial systems and causing the fast-spinning centrifuges to tear themselves apart.[5] Stuxnet’s design and architecture are not domain-specific and it could be tailored as a platform for attacking modern SCADA and PLC systems (e.g., in automobile or power plants), the majority of which reside in Europe, Japan and the US.[6] Stuxnet reportedly ruined almost one-fifth of Iran's nuclear centrifuges.[7]
Stuxnet has three modules: a worm that executes all routines related to the main payload of the attack; a link file that automatically executes the propagated copies of the worm; and a rootkit component responsible for hiding all malicious files and processes, preventing detection of the presence of Stuxnet.[8]
Stuxnet is typically introduced to the target environment via an infected USB flash drive. The worm then propagates across the network, scanning for Siemens Step7 software on computers controlling a PLC. In the absence of either criterion, Stuxnet becomes dormant inside the computer. If both the conditions are fulfilled, Stuxnet introduces the infected rootkit onto the PLC and Step7 software, modifying the codes and giving unexpected commands to the PLC while returning a loop of normal operations system values feedback to the users.[9][10]
In 2015, Kaspersky's research findings on another highly sophisticated espionage platform created by what they called the Equation Group, noted that the group had used two of the same zero-day attacks used by Stuxnet, before they were used in Stuxnet, and their use in both programs was similar. The researchers reported that "the similar type of usage of both exploits together in different computer worms, at around the same time, indicates that the EQUATION group and the Stuxnet developers are either the same or working closely together".[11]:13
The worm initially spreads indiscriminately, but includes a highly specialized malware payload that is designed to target only Siemens supervisory control and data acquisition (SCADA) systems that are configured to control and monitor specific industrial processes.[16][17] Stuxnet infects PLCs by subverting the Step-7 software application that is used to reprogram these devices.[18][19]
Different variants of Stuxnet targeted five Iranian organizations,[20] with the probable target widely suspected to be uranium enrichment infrastructure in Iran;[19][21][22] Symantec noted in August 2010 that 60% of the infected computers worldwide were in Iran.[23] Siemens stated that the worm has not caused any damage to its customers,[24] but the Iran nuclear program, which uses embargoed Siemens equipment procured secretly, has been damaged by Stuxnet.[25][26] Kaspersky Lab concluded that the sophisticated attack could only have been conducted "with nation-state support".[27] This was further supported by the F-Secure's chief researcher Mikko Hyppönen who commented in a Stuxnet FAQ, "That's what it would look like, yes".[28]
In May 2011, the PBS program Need To Know cited a statement by Gary Samore, White House Coordinator for Arms Control and Weapons of Mass Destruction, in which he said, "we're glad they [the Iranians] are having trouble with their centrifuge machine and that we – the US and its allies – are doing everything we can to make sure that we complicate matters for them", offering "winking acknowledgement" of US involvement in Stuxnet.[29] According to The Daily Telegraph, a showreel that was played at a retirement party for the head of the Israel Defense Forces (IDF), Gabi Ashkenazi, included references to Stuxnet as one of his operational successes as the IDF chief of staff.[30]
On 1 June 2012, an article in The New York Times said that Stuxnet is part of a US and Israeli intelligence operation called "Operation Olympic Games", started under President George W. Bush and expanded under President Barack Obama.[31]
On 24 July 2012, an article by Chris Matyszczyk from CNET[32] reported how the Atomic Energy Organization of Iran e-mailed F-Secure's chief research officer Mikko Hyppönen to report a new instance of malware.
On 25 December 2012, an Iranian semi-official news agency announced there was a cyberattack by Stuxnet, this time on the industries in the southern area of the country. The virus targeted a power plant and some other industries in Hormozgan province in recent months.[33]
According to expert Eugene Kaspersky, the worm also infected a nuclear powerplant in Russia. Kaspersky noted, however, that since the powerplant is not connected to the public Internet, the system should remain safe.[34]
Kaspersky Lab experts at first estimated that Stuxnet started spreading around March or April 2010,[41] but the first variant of the worm appeared in June 2009.[18] On 15 July 2010, the day the worm's existence became widely known, a distributed denial-of-service attack was made on the servers for two leading mailing lists on industrial-systems security. This attack, from an unknown source but likely related to Stuxnet, disabled one of the lists and thereby interrupted an important source of information for power plants and factories.[36] On the other hand, researchers at Symantec have uncovered a version of the Stuxnet computer virus that was used to attack Iran's nuclear program in November 2007, being developed as early as 2005, when Iran was still setting up its uranium enrichment facility.[42]
The second variant, with substantial improvements, appeared in March 2010, apparently because its authors believed that Stuxnet was not spreading fast enough; a third, with minor improvements, appeared in April 2010.[36] The worm contains a component with a build time-stamp from 3 February 2010.[43] In the United Kingdom on 25 November 2010, Sky News reported that it had received information from an anonymous source at an unidentified IT security organization that Stuxnet, or a variation of the worm, had been traded on the black market.[44]
Iran was reported to have "beefed up" its cyberwar capabilities
following the Stuxnet attack, and has been suspected of retaliatory
attacks against US banks.[46]
Unlike most malware, Stuxnet does little harm to computers and
networks that do not meet specific configuration requirements; "The
attackers took great care to make sure that only their designated
targets were hit... It was a marksman’s job."[47]
While the worm is promiscuous, it makes itself inert if Siemens
software is not found on infected computers, and contains safeguards to
prevent each infected computer from spreading the worm to more than
three others, and to erase itself on 24 June 2012.[36]
For its targets, Stuxnet contains, among other things, code for a man-in-the-middle attack that fakes industrial process control sensor signals so an infected system does not shut down due to detected abnormal behavior.[36][47][48] Such complexity is very unusual for malware. The worm consists of a layered attack against three different systems:
The malware has both user-mode and kernel-mode rootkit capability under Windows,[53] and its device drivers have been digitally signed with the private keys of two certificates that were stolen from separate well-known companies, JMicron and Realtek, both located at Hsinchu Science Park in Taiwan.[43][51] The driver signing helped it install kernel-mode rootkit drivers successfully without users being notified, and therefore it remained undetected for a relatively long period of time.[57] Both compromised certificates have been revoked by VeriSign.
Two websites in Denmark and Malaysia were configured as command and control servers for the malware, allowing it to be updated, and for industrial espionage to be conducted by uploading information. Both of these websites have subsequently been taken down as part of a global effort to disable the malware.[53][36]
The malware furthermore used a zero-day exploit in the WinCC/SCADA database software in the form of a hard-coded database password.[61]
The entirety of the Stuxnet code has not yet been disclosed, but its
payload targets only those SCADA configurations that meet criteria that
it is programmed to identify.[36]
Stuxnet requires specific slave variable-frequency drives (frequency converter drives) to be attached to the targeted Siemens S7-300 system and its associated modules. It only attacks those PLC systems with variable-frequency drives from two specific vendors: Vacon based in Finland and Fararo Paya based in Iran.[62] Furthermore, it monitors the frequency of the attached motors, and only attacks systems that spin between 807 Hz and 1210 Hz. The industrial applications of motors with these parameters are diverse, and may include pumps or gas centrifuges.
Stuxnet installs malware into memory block DB890 of the PLC that monitors the Profibus messaging bus of the system.[53] When certain criteria are met, it periodically modifies the frequency to 1410 Hz and then to 2 Hz and then to 1064 Hz, and thus affects the operation of the connected motors by changing their rotational speed.[62] It also installs a rootkit – the first such documented case on this platform – that hides the malware on the system and masks the changes in rotational speed from monitoring systems.
The worm's ability to reprogram external PLCs may complicate the removal procedure. Symantec's Liam O'Murchu warns that fixing Windows systems may not completely solve the infection; a thorough audit of PLCs may be necessary. Despite speculation that incorrect removal of the worm could cause damage,[65] Siemens reports that in the first four months since discovery, the malware was successfully removed from the systems of 22 customers without any adverse impact.[63][66]
The US Department of Homeland Security National Cyber Security Division (NCSD) operates the Control System Security Program (CSSP).[68] The program operates a specialized computer emergency response team called the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT), conducts a biannual conference (ICSJWG), provides training, publishes recommended practices, and provides a self-assessment tool. As part of a Department of Homeland Security plan to improve American computer security, in 2008 it and the Idaho National Laboratory (INL) worked with Siemens to identify security holes in the company's widely used Process Control System 7 (PCS 7) and its software Step 7. In July 2008, INL and Siemens publicly announced flaws in the control system at a Chicago conference; Stuxnet exploited these holes in 2009.[47]
Several industry organizations[69][70] and professional societies[71][72] have published standards and best practice guidelines providing direction and guidance for control system end-users on how to establish a control system security management program. The basic premise that all of these documents share is that prevention requires a multi-layered approach, often referred to as "defense-in-depth".[73] The layers include policies and procedures, awareness and training, network segmentation, access control measures, physical security measures, system hardening, e.g., patch management, and system monitoring, anti-virus and intrusion prevention system (IPS). The standards and best practices[who?] also all[improper synthesis?] recommend starting with a risk analysis and a control system security assessment.[74][75]
According to the Israeli newspaper Haaretz, in September 2010 experts on Iran and computer security specialists were increasingly convinced that Stuxnet was meant "to sabotage
the uranium enrichment facility at Natanz – where the centrifuge
operational capacity has dropped over the past year by 30 percent."[87]
On 23 November 2010 it was announced that uranium enrichment at Natanz
had ceased several times because of a series of major technical
problems.[88][89] A "serious nuclear accident" (supposedly the shutdown of some of its centrifuges[90])
occurred at the site in the first half of 2009, which is speculated to
have forced the head of Iran's Atomic Energy Organization Gholam Reza Aghazadeh to resign.[91] Statistics published by the Federation of American Scientists
(FAS) show that the number of enrichment centrifuges operational in
Iran mysteriously declined from about 4,700 to about 3,900 beginning
around the time the nuclear incident WikiLeaks mentioned would have
occurred.[92] The Institute for Science and International Security (ISIS) suggests, in a report published in December 2010, that Stuxnet is "a reasonable explanation for the apparent damage"[93]
at Natanz, and may have destroyed up to 1000 centrifuges (10 percent)
sometime between November 2009 and late January 2010. The authors
conclude:
The worm worked by first causing an infected Iranian IR-1 centrifuge to increase from its normal operating speed of 1,064 hertz to 1,410 hertz for 15 minutes before returning to its normal frequency. Twenty-seven days later, the worm went back into action, slowing the infected centrifuges down to a few hundred hertz for a full 50 minutes. The stresses from the excessive, then slower, speeds caused the aluminum centrifugal tubes to expand, often forcing parts of the centrifuges into sufficient contact with each other to destroy the machine.[95]
According to The Washington Post, IAEA cameras installed in the Natanz facility recorded the sudden dismantling and removal of approximately 900–1000 centrifuges during the time the Stuxnet worm was reportedly active at the plant. Iranian technicians, however, were able to quickly replace the centrifuges and the report concluded that uranium enrichment was likely only briefly disrupted.[96]
On 15 February 2011, ISIS released a report concluding that:
The head of the Bushehr Nuclear Power Plant told Reuters that only the personal computers of staff at the plant had been infected by Stuxnet and the state-run newspaper Iran Daily quoted Reza Taghipour, Iran's telecommunications minister, as saying that it had not caused "serious damage to government systems".[77] The Director of Information Technology Council at the Iranian Ministry of Industries and Mines, Mahmud Liaii, has said that: "An electronic war has been launched against Iran... This computer worm is designed to transfer data about production lines from our industrial plants to locations outside Iran."[99]
In response to the infection, Iran has assembled a team to combat it. With more than 30,000 IP addresses affected in Iran, an official has said that the infection is fast spreading in Iran and the problem has been compounded by the ability of Stuxnet to mutate. Iran has set up its own systems to clean up infections and has advised against using the Siemens SCADA antivirus since it is suspected that the antivirus is actually embedded with codes which update Stuxnet instead of eradicating it.[100][101][102][103]
According to Hamid Alipour, deputy head of Iran's government Information Technology Company, "The attack is still ongoing and new versions of this virus are spreading." He reports that his company had begun the cleanup process at Iran's "sensitive centres and organizations."[101] "We had anticipated that we could root out the virus within one to two months, but the virus is not stable, and since we started the cleanup process three new versions of it have been spreading", he told the Islamic Republic News Agency on 27 September 2010.[103]
On 29 November 2010, Iranian president Mahmoud Ahmadinejad stated for the first time that a computer virus had caused problems with the controller handling the centrifuges at its Natanz facilities. According to Reuters he told reporters at a news conference in Tehran, "They succeeded in creating problems for a limited number of our centrifuges with the software they had installed in electronic parts."[104][105]
On the same day two Iranian nuclear scientists were targeted in separate, but nearly simultaneous car bomb attacks near Shahid Beheshti University in Tehran. Majid Shahriari, a quantum physicist was killed. Fereydoon Abbasi, a high-ranking official at the Ministry of Defense was seriously wounded. Wired speculated that the assassinations could indicate that whoever was behind Stuxnet felt that it was not sufficient to stop the nuclear program.[106] In January 2010, another Iranian nuclear scientist, a physics professor at Tehran University, had been killed in a similar bomb explosion.[106] On 11 January 2012, a Director of the Natanz nuclear enrichment facility, Mostafa Ahmadi Roshan, was killed in an attack quite similar to the one that killed Shahriari.[107]
An analysis by the FAS demonstrates that Iran’s enrichment capacity grew during 2010. The study indicates that Iran’s centrifuges appear to be performing 60% better than in the previous year, which would significantly reduce Tehran’s time to produce bomb-grade uranium. The FAS report was reviewed by an official with the IAEA who affirmed the study.[108][109][110]
European and US officials, along with private experts, have told Reuters that Iranian engineers were successful in neutralizing and purging Stuxnet from their country's nuclear machinery.[111]
Given the growth in Iranian enrichment capability in 2010, the country may have intentionally put out misinformation to cause Stuxnet's creators to believe that the worm was more successful in disabling the Iranian nuclear program than it actually was.[36]
In 2009, a year before Stuxnet was discovered, Scott Borg of the United States Cyber-Consequences Unit (US-CCU)[121] suggested that Israel might prefer to mount a cyber-attack rather than a military strike on Iran's nuclear facilities.[98] And, in late 2010 Borg stated, "Israel certainly has the ability to create Stuxnet and there is little downside to such an attack, because it would be virtually impossible to prove who did it. So a tool like Stuxnet is Israel's obvious weapon of choice."[122] Iran uses P-1 centrifuges at Natanz, the design for which A. Q. Khan stole in 1976 and took to Pakistan. His black market nuclear-proliferation network sold P-1s to, among other customers, Iran. Experts believe that Israel also somehow acquired P-1s and tested Stuxnet on the centrifuges, installed at the Dimona facility that is part of its own nuclear program.[47] The equipment may be from the United States, which received P-1s from Libya's former nuclear program.[123][47]
Some have also referred to several clues in the code such as a concealed reference to the word "MYRTUS", believed to refer to the Myrtle tree, or Hadassah in Hebrew. Hadassah was the birth name of the former Jewish queen of Persia, Queen Esther.[124][125] However, it may be that the "MYRTUS" reference is simply a misinterpreted reference to SCADA components known as RTUs (Remote Terminal Units) and that this reference is actually "My RTUs"–a management feature of SCADA.[126] Also, the number 19790509 appears once in the code and might refer to the date "1979 May 09", the day Habib Elghanian, a Persian Jew, was executed in Tehran.[53][127][128] Another date that appears in the code is "24 September 2007", the day that Iran's president Mahmoud Ahmadinejad spoke at Columbia University and made comments questioning the validity of the Holocaust.[36] Such data is not conclusive, since, as written by Symantec, "Attackers would have the natural desire to implicate another party" with a false flag.[36][53]
In a March 2012 interview with CBS News' "60 Minutes", retired USAF General Michael Hayden – who served as director of both the Central Intelligence Agency and National Security Agency – while denying knowledge of who created Stuxnet said that he believed it had been "a good idea" but that it carried a downside in that it had legitimized the use of sophisticated cyberweapons designed to cause physical damage. Hayden said, "There are those out there who can take a look at this... and maybe even attempt to turn it to their own purposes". In the same report, Sean McGurk, a former cybersecurity official at the Department of Homeland Security noted that the Stuxnet source code could now be downloaded online and modified to be directed at new target systems. Speaking of the Stuxnet creators, he said, "They opened the box. They demonstrated the capability... It's not something that can be put back."[136]
John P. Wheeler III, a lawyer attached to the Office of the Secretary of the Air Force, conducted a close review of prevailing legal authorities to engage in nation-state offensive cyberwarfare, concluded that such use was a belligerent "act of war," and argued against a then-pending proposal to transfer offensive cyberwarfare command authority from USSTRATCOM to NSA; raising questions about the legality of the alleged US deployment of Stuxnet within the legal framework current at the time of the attack. Wheeler was murdered in December 2010 under mysterious circumstances.[137]
In April 2011 Iranian government official Gholam Reza Jalali stated
that an investigation had concluded that the United States and Israel
were behind the Stuxnet attack.[138] According to Vanity Fair,
Rieger stated that three European countries' intelligence agencies
agreed that Stuxnet was a joint United States-Israel effort. The code
for the Windows injector and the PLC payload differ in style, likely
implying collaboration. Other experts believe that a US-Israel
cooperation is unlikely because "the level of trust between the two
countries’ intelligence and military establishments is not high."[36]
A Wired magazine article about US General Keith B. Alexander stated: "And he and his cyberwarriors have already launched their first attack. The cyberweapon that came to be known as Stuxnet was created and built by the NSA in partnership with the CIA and Israeli intelligence in the mid-2000s."[139]
China,[140] Jordan, and France are other possibilities, and Siemens may have also participated.[36][129] Langner speculated that the infection may have spread from USB drives belonging to Russian contractors since the Iranian targets were not accessible via the internet.[19][141]
Sandro Gaycken from the Free University Berlin argued that the attack on Iran was a ruse to distract from Stuxnet's real purpose. According to him, its broad dissemination in more than 100,000 industrial plants worldwide suggests a field test of a cyber weapon in different security cultures, testing their preparedness, resilience, and reactions, all highly valuable information for a cyberwar unit.[142]
The United Kingdom has denied involvement in the virus's creation.[143]
Stratfor Documents released by Wikileaks suggest that the International Security Firm 'Stratfor' believe that Israel is behind Stuxnet - "But we can't assume that because they did stuxnet that they are capable of doing this blast as well".[144]
In July 2013, Edward Snowden claimed that Stuxnet was cooperatively developed by the United States and Israel.[145]
Stuxnet specifically targets PLCs, which allow the automation of electromechanical processes such as those used to control machinery on factory assembly lines, amusement rides, or centrifuges for separating nuclear material. Exploiting four zero-day flaws,[4] Stuxnet functions by targeting machines using the Microsoft Windows operating system and networks, then seeking out Siemens Step7 software. Stuxnet reportedly compromised Iranian PLCs, collecting information on industrial systems and causing the fast-spinning centrifuges to tear themselves apart.[5] Stuxnet’s design and architecture are not domain-specific and it could be tailored as a platform for attacking modern SCADA and PLC systems (e.g., in automobile or power plants), the majority of which reside in Europe, Japan and the US.[6] Stuxnet reportedly ruined almost one-fifth of Iran's nuclear centrifuges.[7]
Stuxnet has three modules: a worm that executes all routines related to the main payload of the attack; a link file that automatically executes the propagated copies of the worm; and a rootkit component responsible for hiding all malicious files and processes, preventing detection of the presence of Stuxnet.[8]
Stuxnet is typically introduced to the target environment via an infected USB flash drive. The worm then propagates across the network, scanning for Siemens Step7 software on computers controlling a PLC. In the absence of either criterion, Stuxnet becomes dormant inside the computer. If both the conditions are fulfilled, Stuxnet introduces the infected rootkit onto the PLC and Step7 software, modifying the codes and giving unexpected commands to the PLC while returning a loop of normal operations system values feedback to the users.[9][10]
In 2015, Kaspersky's research findings on another highly sophisticated espionage platform created by what they called the Equation Group, noted that the group had used two of the same zero-day attacks used by Stuxnet, before they were used in Stuxnet, and their use in both programs was similar. The researchers reported that "the similar type of usage of both exploits together in different computer worms, at around the same time, indicates that the EQUATION group and the Stuxnet developers are either the same or working closely together".[11]:13
Contents
Discovery
Stuxnet initially spread via Microsoft Windows, and targeted Siemens industrial control systems. While it is not the first time that hackers have targeted industrial systems,[12] nor the first publicly known intentional act of cyberwarfare to be implemented, it is the first discovered malware that spies on and subverts industrial systems,[13] and the first to include a programmable logic controller (PLC) rootkit.[14][15]The worm initially spreads indiscriminately, but includes a highly specialized malware payload that is designed to target only Siemens supervisory control and data acquisition (SCADA) systems that are configured to control and monitor specific industrial processes.[16][17] Stuxnet infects PLCs by subverting the Step-7 software application that is used to reprogram these devices.[18][19]
Different variants of Stuxnet targeted five Iranian organizations,[20] with the probable target widely suspected to be uranium enrichment infrastructure in Iran;[19][21][22] Symantec noted in August 2010 that 60% of the infected computers worldwide were in Iran.[23] Siemens stated that the worm has not caused any damage to its customers,[24] but the Iran nuclear program, which uses embargoed Siemens equipment procured secretly, has been damaged by Stuxnet.[25][26] Kaspersky Lab concluded that the sophisticated attack could only have been conducted "with nation-state support".[27] This was further supported by the F-Secure's chief researcher Mikko Hyppönen who commented in a Stuxnet FAQ, "That's what it would look like, yes".[28]
In May 2011, the PBS program Need To Know cited a statement by Gary Samore, White House Coordinator for Arms Control and Weapons of Mass Destruction, in which he said, "we're glad they [the Iranians] are having trouble with their centrifuge machine and that we – the US and its allies – are doing everything we can to make sure that we complicate matters for them", offering "winking acknowledgement" of US involvement in Stuxnet.[29] According to The Daily Telegraph, a showreel that was played at a retirement party for the head of the Israel Defense Forces (IDF), Gabi Ashkenazi, included references to Stuxnet as one of his operational successes as the IDF chief of staff.[30]
On 1 June 2012, an article in The New York Times said that Stuxnet is part of a US and Israeli intelligence operation called "Operation Olympic Games", started under President George W. Bush and expanded under President Barack Obama.[31]
On 24 July 2012, an article by Chris Matyszczyk from CNET[32] reported how the Atomic Energy Organization of Iran e-mailed F-Secure's chief research officer Mikko Hyppönen to report a new instance of malware.
On 25 December 2012, an Iranian semi-official news agency announced there was a cyberattack by Stuxnet, this time on the industries in the southern area of the country. The virus targeted a power plant and some other industries in Hormozgan province in recent months.[33]
According to expert Eugene Kaspersky, the worm also infected a nuclear powerplant in Russia. Kaspersky noted, however, that since the powerplant is not connected to the public Internet, the system should remain safe.[34]
History
The worm was at first identified by the security company VirusBlokAda in mid-June 2010.[18] Journalist Brian Krebs's blog posting on 15 July 2010 was the first widely read report on the worm.[35][36] The original name given by VirusBlokAda was "Rootkit.Tmphider";[37] Symantec however called it "W32.Temphid", later changing to "W32.Stuxnet".[38] Its current name is derived from a combination of some keywords in the software (".stub" and "mrxnet.sys").[39][40] The reason for the discovery at this time is attributed to the virus accidentally spreading beyond its intended target (the Natanz plant) due to a programming error introduced in an update; this led to the worm spreading to an engineer's computer that had been connected to the centrifuges, and spreading further when the engineer returned home and connected his computer to the internet.[31]Kaspersky Lab experts at first estimated that Stuxnet started spreading around March or April 2010,[41] but the first variant of the worm appeared in June 2009.[18] On 15 July 2010, the day the worm's existence became widely known, a distributed denial-of-service attack was made on the servers for two leading mailing lists on industrial-systems security. This attack, from an unknown source but likely related to Stuxnet, disabled one of the lists and thereby interrupted an important source of information for power plants and factories.[36] On the other hand, researchers at Symantec have uncovered a version of the Stuxnet computer virus that was used to attack Iran's nuclear program in November 2007, being developed as early as 2005, when Iran was still setting up its uranium enrichment facility.[42]
The second variant, with substantial improvements, appeared in March 2010, apparently because its authors believed that Stuxnet was not spreading fast enough; a third, with minor improvements, appeared in April 2010.[36] The worm contains a component with a build time-stamp from 3 February 2010.[43] In the United Kingdom on 25 November 2010, Sky News reported that it had received information from an anonymous source at an unidentified IT security organization that Stuxnet, or a variation of the worm, had been traded on the black market.[44]
Affected countries
A study of the spread of Stuxnet by Symantec showed that the main affected countries in the early days of the infection were Iran, Indonesia and India:[45]| Country | Infected computers |
|---|---|
| Iran | 58.85% |
| Indonesia | 18.22% |
| India | 8.31% |
| Azerbaijan | 2.57% |
| United States | 1.56% |
| Pakistan | 1.28% |
| Others | 9.2% |
Operation
| “ | [O]ne of the great technical blockbusters in malware history. | ” |
|
— Vanity Fair, April 2011[36]
|
||
For its targets, Stuxnet contains, among other things, code for a man-in-the-middle attack that fakes industrial process control sensor signals so an infected system does not shut down due to detected abnormal behavior.[36][47][48] Such complexity is very unusual for malware. The worm consists of a layered attack against three different systems:
- The Windows operating system,
- Siemens PCS 7, WinCC and STEP7 industrial software applications that run on Windows and
- One or more Siemens S7 PLCs.
Windows infection
Stuxnet attacked Windows systems using an unprecedented four zero-day attacks (plus the CPLINK vulnerability and a vulnerability used by the Conficker worm[49]). It is initially spread using infected removable drives such as USB flash drives,[19][50] and then uses other exploits and techniques such as peer-to-peer RPC to infect and update other computers inside private networks that are not directly connected to the Internet.[51][52][53] The number of zero-day exploits used is unusual, as they are highly valued and malware creators do not normally waste the use of four different ones in the same worm.[21] Amongst these exploits were remotely code execution on a computer with Printer Sharing enabled,[54] and the LNK/PIF vulnerability,[55] in which file execution is accomplished when an icon is viewed in Windows Explorer; negating the need for user interaction.[56] Stuxnet is unusually large at half a megabyte in size,[51] and written in several different programming languages (including C and C++) which is also irregular for malware.[13][18][48] The Windows component of the malware is promiscuous in that it spreads relatively quickly and indiscriminately.[43]The malware has both user-mode and kernel-mode rootkit capability under Windows,[53] and its device drivers have been digitally signed with the private keys of two certificates that were stolen from separate well-known companies, JMicron and Realtek, both located at Hsinchu Science Park in Taiwan.[43][51] The driver signing helped it install kernel-mode rootkit drivers successfully without users being notified, and therefore it remained undetected for a relatively long period of time.[57] Both compromised certificates have been revoked by VeriSign.
Two websites in Denmark and Malaysia were configured as command and control servers for the malware, allowing it to be updated, and for industrial espionage to be conducted by uploading information. Both of these websites have subsequently been taken down as part of a global effort to disable the malware.[53][36]
Step 7 software infection
According to researcher Ralph Langner,[58][59] once installed on a Windows system Stuxnet infects project files belonging to Siemens' WinCC/PCS 7 SCADA control software[60] (Step 7), and subverts a key communication library of WinCC calleds7otbxdx.dll.
Doing so intercepts communications between the WinCC software running
under Windows and the target Siemens PLC devices that the software is
able to configure and program when the two are connected via a data
cable. In this way, the malware is able to install itself on PLC devices
unnoticed, and subsequently to mask its presence from WinCC if the
control software attempts to read an infected block of memory from the
PLC system.[53]The malware furthermore used a zero-day exploit in the WinCC/SCADA database software in the form of a hard-coded database password.[61]
PLC infection
Siemens Simatic S7-300 PLC CPU with three I/O modules attached
Stuxnet requires specific slave variable-frequency drives (frequency converter drives) to be attached to the targeted Siemens S7-300 system and its associated modules. It only attacks those PLC systems with variable-frequency drives from two specific vendors: Vacon based in Finland and Fararo Paya based in Iran.[62] Furthermore, it monitors the frequency of the attached motors, and only attacks systems that spin between 807 Hz and 1210 Hz. The industrial applications of motors with these parameters are diverse, and may include pumps or gas centrifuges.
Stuxnet installs malware into memory block DB890 of the PLC that monitors the Profibus messaging bus of the system.[53] When certain criteria are met, it periodically modifies the frequency to 1410 Hz and then to 2 Hz and then to 1064 Hz, and thus affects the operation of the connected motors by changing their rotational speed.[62] It also installs a rootkit – the first such documented case on this platform – that hides the malware on the system and masks the changes in rotational speed from monitoring systems.
Removal
Siemens has released a detection and removal tool for Stuxnet. Siemens recommends contacting customer support if an infection is detected and advises installing Microsoft updates for security vulnerabilities and prohibiting the use of third-party USB flash drives.[63] Siemens also advises immediately upgrading password access codes.[64]The worm's ability to reprogram external PLCs may complicate the removal procedure. Symantec's Liam O'Murchu warns that fixing Windows systems may not completely solve the infection; a thorough audit of PLCs may be necessary. Despite speculation that incorrect removal of the worm could cause damage,[65] Siemens reports that in the first four months since discovery, the malware was successfully removed from the systems of 22 customers without any adverse impact.[63][66]
Control system security
Main article: Control system security
Prevention of control system security incidents,[67] such as from viral infections like Stuxnet, is a topic that is being addressed in both the public and the private sector.The US Department of Homeland Security National Cyber Security Division (NCSD) operates the Control System Security Program (CSSP).[68] The program operates a specialized computer emergency response team called the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT), conducts a biannual conference (ICSJWG), provides training, publishes recommended practices, and provides a self-assessment tool. As part of a Department of Homeland Security plan to improve American computer security, in 2008 it and the Idaho National Laboratory (INL) worked with Siemens to identify security holes in the company's widely used Process Control System 7 (PCS 7) and its software Step 7. In July 2008, INL and Siemens publicly announced flaws in the control system at a Chicago conference; Stuxnet exploited these holes in 2009.[47]
Several industry organizations[69][70] and professional societies[71][72] have published standards and best practice guidelines providing direction and guidance for control system end-users on how to establish a control system security management program. The basic premise that all of these documents share is that prevention requires a multi-layered approach, often referred to as "defense-in-depth".[73] The layers include policies and procedures, awareness and training, network segmentation, access control measures, physical security measures, system hardening, e.g., patch management, and system monitoring, anti-virus and intrusion prevention system (IPS). The standards and best practices[who?] also all[improper synthesis?] recommend starting with a risk analysis and a control system security assessment.[74][75]
Target and origin
Experts believe that Stuxnet required the largest and costliest development effort in malware history.[36] Developing its many capabilities would have required a team of highly capable programmers, in-depth knowledge of industrial processes, and an interest in attacking industrial infrastructure.[13][18] Eric Byres, who has years of experience maintaining and troubleshooting Siemens systems, told Wired that writing the code would have taken many man-months, if not years.[51] Symantec estimates that the group developing Stuxnet would have consisted of anywhere from five to thirty people, and would have taken six months to prepare.[76][36] The Guardian, the BBC and The New York Times all claimed that (unnamed) experts studying Stuxnet believe the complexity of the code indicates that only a nation-state would have the capabilities to produce it.[21][76][77] The self-destruct and other safeguards within the code imply that a Western government was responsible, with lawyers evaluating the worm's ramifications.[36] Software security expert Bruce Schneier initially condemned the 2010 news coverage of Stuxnet as hype, however, stating that it was almost entirely based on speculation.[78] But after subsequent research, Schneier stated in 2012 that "we can now conclusively link Stuxnet to the centrifuge structure at the Natanz nuclear enrichment lab in Iran".[79]Iran as target
Ralph Langner, the researcher who identified that Stuxnet infected PLCs,[19] first speculated publicly in September 2010 that the malware was of Israeli origin, and that it targeted Iranian nuclear facilities.[80] However Langner more recently, in a TED Talk recorded in February 2011, stated that, "My opinion is that the Mossad is involved, but that the leading force is not Israel. The leading force behind Stuxnet is the cyber superpower – there is only one; and that's the United States."[81] Kevin Hogan, Senior Director of Security Response at Symantec, reported that the majority of infected systems were in Iran (about 60%),[82] which has led to speculation that it may have been deliberately targeting "high-value infrastructure" in Iran[21] including either the Bushehr Nuclear Power Plant or the Natanz nuclear facility.[51][83][84] Langner called the malware "a one-shot weapon" and said that the intended target was probably hit,[85] although he admitted this was speculation.[51] Another German researcher, Frank Rieger, was the first to speculate that Natanz was the target.[36]Natanz nuclear facilities
Anti-aircraft guns guarding Natanz Nuclear Facility
The attacks seem designed to force a change in the centrifuge’s rotor speed, first raising the speed and then lowering it, likely with the intention of inducing excessive vibrations or distortions that would destroy the centrifuge. If its goal was to quickly destroy all the centrifuges in the FEP [Fuel Enrichment Plant], Stuxnet failed. But if the goal was to destroy a more limited number of centrifuges and set back Iran’s progress in operating the FEP, while making detection difficult, it may have succeeded, at least temporarily.[93]The ISIS report further notes that Iranian authorities have attempted to conceal the breakdown by installing new centrifuges on a large scale.[93][94]
The worm worked by first causing an infected Iranian IR-1 centrifuge to increase from its normal operating speed of 1,064 hertz to 1,410 hertz for 15 minutes before returning to its normal frequency. Twenty-seven days later, the worm went back into action, slowing the infected centrifuges down to a few hundred hertz for a full 50 minutes. The stresses from the excessive, then slower, speeds caused the aluminum centrifugal tubes to expand, often forcing parts of the centrifuges into sufficient contact with each other to destroy the machine.[95]
According to The Washington Post, IAEA cameras installed in the Natanz facility recorded the sudden dismantling and removal of approximately 900–1000 centrifuges during the time the Stuxnet worm was reportedly active at the plant. Iranian technicians, however, were able to quickly replace the centrifuges and the report concluded that uranium enrichment was likely only briefly disrupted.[96]
On 15 February 2011, ISIS released a report concluding that:
Assuming Iran exercises caution, Stuxnet is unlikely to destroy more centrifuges at the Natanz plant. Iran likely cleaned the malware from its control systems. To prevent re-infection, Iran will have to exercise special caution since so many computers in Iran contain Stuxnet.
Although Stuxnet appears to be designed to destroy centrifuges at the Natanz facility, destruction was by no means total. Moreover, Stuxnet did not lower the production of LEU during 2010. LEU quantities could have certainly been greater, and Stuxnet could be an important part of the reason why they did not increase significantly. Nonetheless, there remain important questions about why Stuxnet destroyed only 1,000 centrifuges. One observation is that it may be harder to destroy centrifuges by use of cyber attacks than often believed.[93]
Iranian reaction
The Associated Press reported that the semi-official Iranian Students News Agency released a statement on 24 September 2010 stating that experts from the Atomic Energy Organization of Iran met in the previous week to discuss how Stuxnet could be removed from their systems.[17] According to analysts, such as David Albright, Western intelligence agencies have been attempting to sabotage the Iranian nuclear program for some time.[97][98]The head of the Bushehr Nuclear Power Plant told Reuters that only the personal computers of staff at the plant had been infected by Stuxnet and the state-run newspaper Iran Daily quoted Reza Taghipour, Iran's telecommunications minister, as saying that it had not caused "serious damage to government systems".[77] The Director of Information Technology Council at the Iranian Ministry of Industries and Mines, Mahmud Liaii, has said that: "An electronic war has been launched against Iran... This computer worm is designed to transfer data about production lines from our industrial plants to locations outside Iran."[99]
In response to the infection, Iran has assembled a team to combat it. With more than 30,000 IP addresses affected in Iran, an official has said that the infection is fast spreading in Iran and the problem has been compounded by the ability of Stuxnet to mutate. Iran has set up its own systems to clean up infections and has advised against using the Siemens SCADA antivirus since it is suspected that the antivirus is actually embedded with codes which update Stuxnet instead of eradicating it.[100][101][102][103]
According to Hamid Alipour, deputy head of Iran's government Information Technology Company, "The attack is still ongoing and new versions of this virus are spreading." He reports that his company had begun the cleanup process at Iran's "sensitive centres and organizations."[101] "We had anticipated that we could root out the virus within one to two months, but the virus is not stable, and since we started the cleanup process three new versions of it have been spreading", he told the Islamic Republic News Agency on 27 September 2010.[103]
On 29 November 2010, Iranian president Mahmoud Ahmadinejad stated for the first time that a computer virus had caused problems with the controller handling the centrifuges at its Natanz facilities. According to Reuters he told reporters at a news conference in Tehran, "They succeeded in creating problems for a limited number of our centrifuges with the software they had installed in electronic parts."[104][105]
On the same day two Iranian nuclear scientists were targeted in separate, but nearly simultaneous car bomb attacks near Shahid Beheshti University in Tehran. Majid Shahriari, a quantum physicist was killed. Fereydoon Abbasi, a high-ranking official at the Ministry of Defense was seriously wounded. Wired speculated that the assassinations could indicate that whoever was behind Stuxnet felt that it was not sufficient to stop the nuclear program.[106] In January 2010, another Iranian nuclear scientist, a physics professor at Tehran University, had been killed in a similar bomb explosion.[106] On 11 January 2012, a Director of the Natanz nuclear enrichment facility, Mostafa Ahmadi Roshan, was killed in an attack quite similar to the one that killed Shahriari.[107]
An analysis by the FAS demonstrates that Iran’s enrichment capacity grew during 2010. The study indicates that Iran’s centrifuges appear to be performing 60% better than in the previous year, which would significantly reduce Tehran’s time to produce bomb-grade uranium. The FAS report was reviewed by an official with the IAEA who affirmed the study.[108][109][110]
European and US officials, along with private experts, have told Reuters that Iranian engineers were successful in neutralizing and purging Stuxnet from their country's nuclear machinery.[111]
Given the growth in Iranian enrichment capability in 2010, the country may have intentionally put out misinformation to cause Stuxnet's creators to believe that the worm was more successful in disabling the Iranian nuclear program than it actually was.[36]
Israel
Israel, through Unit 8200,[112][113] has been speculated to be the country behind Stuxnet in many media reports[76][90][114] and by experts such as Richard A. Falkenrath, former Senior Director for Policy and Plans within the US Office of Homeland Security.[115][77] Yossi Melman, who covers intelligence for the Israeli daily newspaper Haaretz and is writing a book about Israeli intelligence, also suspected that Israel was involved, noting that Meir Dagan, the former (up until 2011) head of the national intelligence agency Mossad, had his term extended in 2009 because he was said to be involved in important projects. Additionally, Israel now expects that Iran will have a nuclear weapon in 2014 or 2015 – at least three years later than earlier estimates – without the need for an Israeli military attack on Iranian nuclear facilities; "They seem to know something, that they have more time than originally thought", he added.[26][47] Israel has not publicly commented on the Stuxnet attack but confirmed that cyberwarfare is now among the pillars of its defense doctrine, with a military intelligence unit set up to pursue both defensive and offensive options.[116][117][118] When questioned whether Israel was behind the virus in the fall of 2010, some Israeli officials[who?] broke into "wide smiles", fueling speculation that the government of Israel was involved with its genesis.[119] American presidential advisor Gary Samore also smiled when Stuxnet was mentioned,[47] although American officials have indicated that the virus originated abroad.[119] According to The Telegraph, Israeli newspaper Haaretz reported that a video celebrating operational successes of Gabi Ashkenazi, retiring IDF Chief of Staff, was shown at his retirement party and included references to Stuxnet, thus strengthening claims that Israel's security forces were responsible.[120]In 2009, a year before Stuxnet was discovered, Scott Borg of the United States Cyber-Consequences Unit (US-CCU)[121] suggested that Israel might prefer to mount a cyber-attack rather than a military strike on Iran's nuclear facilities.[98] And, in late 2010 Borg stated, "Israel certainly has the ability to create Stuxnet and there is little downside to such an attack, because it would be virtually impossible to prove who did it. So a tool like Stuxnet is Israel's obvious weapon of choice."[122] Iran uses P-1 centrifuges at Natanz, the design for which A. Q. Khan stole in 1976 and took to Pakistan. His black market nuclear-proliferation network sold P-1s to, among other customers, Iran. Experts believe that Israel also somehow acquired P-1s and tested Stuxnet on the centrifuges, installed at the Dimona facility that is part of its own nuclear program.[47] The equipment may be from the United States, which received P-1s from Libya's former nuclear program.[123][47]
Some have also referred to several clues in the code such as a concealed reference to the word "MYRTUS", believed to refer to the Myrtle tree, or Hadassah in Hebrew. Hadassah was the birth name of the former Jewish queen of Persia, Queen Esther.[124][125] However, it may be that the "MYRTUS" reference is simply a misinterpreted reference to SCADA components known as RTUs (Remote Terminal Units) and that this reference is actually "My RTUs"–a management feature of SCADA.[126] Also, the number 19790509 appears once in the code and might refer to the date "1979 May 09", the day Habib Elghanian, a Persian Jew, was executed in Tehran.[53][127][128] Another date that appears in the code is "24 September 2007", the day that Iran's president Mahmoud Ahmadinejad spoke at Columbia University and made comments questioning the validity of the Holocaust.[36] Such data is not conclusive, since, as written by Symantec, "Attackers would have the natural desire to implicate another party" with a false flag.[36][53]
United States
There has also been testimony on the involvement of the United States and its collaboration with Israel,[129][130] with one report stating that "there is vanishingly little doubt that [it] played a role in creating the worm."[36] It has been reported that the United States, under one of its most secret programs, initiated by the Bush administration and accelerated[citation needed] by the Obama administration, has sought to destroy Iran's nuclear program by novel methods such as undermining Iranian computer systems. A diplomatic cable obtained by WikiLeaks showed how the United States was advised to target Iran's nuclear capabilities through 'covert sabotage'.[131] A New York Times article as early as January 2009 credited a then unspecified program with preventing an Israeli military attack on Iran where some of the efforts focused on ways to destabilize the centrifuges.[132] A Wired article claimed that Stuxnet "is believed to have been created by the United States".[133] The fact that John Bumgarner, a former intelligence officer and member of the United States Cyber-Consequences Unit (US-CCU), published an article prior to Stuxnet being discovered or deciphered, that outlined a strategic cyberstrike on centrifuges[134] and suggests that cyber attacks are permissible against nation states which are operating uranium enrichment programs that violate international treaties gives some credibility to these claims. Bumgarner pointed out that the centrifuges used to process fuel for nuclear weapons are a key target for cybertage operations and that they can be made to destroy themselves by manipulating their rotational speeds.[135]In a March 2012 interview with CBS News' "60 Minutes", retired USAF General Michael Hayden – who served as director of both the Central Intelligence Agency and National Security Agency – while denying knowledge of who created Stuxnet said that he believed it had been "a good idea" but that it carried a downside in that it had legitimized the use of sophisticated cyberweapons designed to cause physical damage. Hayden said, "There are those out there who can take a look at this... and maybe even attempt to turn it to their own purposes". In the same report, Sean McGurk, a former cybersecurity official at the Department of Homeland Security noted that the Stuxnet source code could now be downloaded online and modified to be directed at new target systems. Speaking of the Stuxnet creators, he said, "They opened the box. They demonstrated the capability... It's not something that can be put back."[136]
John P. Wheeler III, a lawyer attached to the Office of the Secretary of the Air Force, conducted a close review of prevailing legal authorities to engage in nation-state offensive cyberwarfare, concluded that such use was a belligerent "act of war," and argued against a then-pending proposal to transfer offensive cyberwarfare command authority from USSTRATCOM to NSA; raising questions about the legality of the alleged US deployment of Stuxnet within the legal framework current at the time of the attack. Wheeler was murdered in December 2010 under mysterious circumstances.[137]
Joint effort and other states and targets
| This section is outdated. (June 2012) |
A Wired magazine article about US General Keith B. Alexander stated: "And he and his cyberwarriors have already launched their first attack. The cyberweapon that came to be known as Stuxnet was created and built by the NSA in partnership with the CIA and Israeli intelligence in the mid-2000s."[139]
China,[140] Jordan, and France are other possibilities, and Siemens may have also participated.[36][129] Langner speculated that the infection may have spread from USB drives belonging to Russian contractors since the Iranian targets were not accessible via the internet.[19][141]
Sandro Gaycken from the Free University Berlin argued that the attack on Iran was a ruse to distract from Stuxnet's real purpose. According to him, its broad dissemination in more than 100,000 industrial plants worldwide suggests a field test of a cyber weapon in different security cultures, testing their preparedness, resilience, and reactions, all highly valuable information for a cyberwar unit.[142]
The United Kingdom has denied involvement in the virus's creation.[143]
Stratfor Documents released by Wikileaks suggest that the International Security Firm 'Stratfor' believe that Israel is behind Stuxnet - "But we can't assume that because they did stuxnet that they are capable of doing this blast as well".[144]
In July 2013, Edward Snowden claimed that Stuxnet was cooperatively developed by the United States and Israel.[145]
Deployment in North Korea
According to a report by Reuters, the NSA also tried to sabotage North Korea's nuclear program using a version of Stuxnet. The operation was reportedly launched in tandem with the attack that targeted Iranian centrifuges in 2009–2010. The North Korean nuclear program shares many similarities with the Iranian, both having been developed with technology transferred by Pakistani nuclear scientist A.Q. Khan. The effort failed, however, because North Korea's extreme secrecy and isolation made it impossible to introduce Stuxnet into the nuclear facility.[146]Related malware
"Stuxnet's Secret Twin"
A November 2013 article[147] in Foreign Policy magazine claims existence of an earlier, much more sophisticated attack on centrifuge complex at Natanz, focused on increasing centrifuge failure rate over long time period via stealthily inducing uranium hexafluoride gas overpressure incidents. This malware was capable of spreading only by being physically installed, probably by previously contaminated field equipment used by contractors working on Siemens control systems of the complex. It is not clear whether this attack attempt was successful, but it being followed by a different, simpler and more conventional attack is indicative.Duqu
Main article: Duqu
On 1 September 2011, a new worm was found, thought to be related to
Stuxnet. The Laboratory of Cryptography and System Security (CrySyS) of
the Budapest University of Technology and Economics analyzed the malware, naming the threat Duqu.[148][149] Symantec,
based on this report, continued the analysis of the threat, calling it
"nearly identical to Stuxnet, but with a completely different purpose",
and published a detailed technical paper.[150] The main component used in Duqu is designed to capture information[48]
such as keystrokes and system information. The exfiltrated data may be
used to enable a future Stuxnet-like attack. On 28 December 2011,
Kaspersky Lab's director of global research and analysis spoke to Reuters
about recent research results showing that the platform Stuxnet and
Duqu both originated from in 2007, and is being referred to as Tilded
due to the ~d at the beginning of the file names. Also uncovered in this
research was the possibility for three more variants based on the
Tilded platform.[151]Flame
Main article: Flame (malware)
In May 2012, the new malware "Flame" was found, thought to be related to Stuxnet.[152] Researchers named the program "Flame" after the name of one of its modules.[152]
After analysing the code of Flame, Kaspersky Lab said that there is a
strong relationship between Flame and Stuxnet. An early version of
Stuxnet contained code to propagate infections via USB drives that is
nearly identical to a Flame module that exploits the same vulnerability.[153]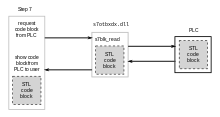




Comments
Post a Comment